Your Data Leaks Are More Common Than You May Realize
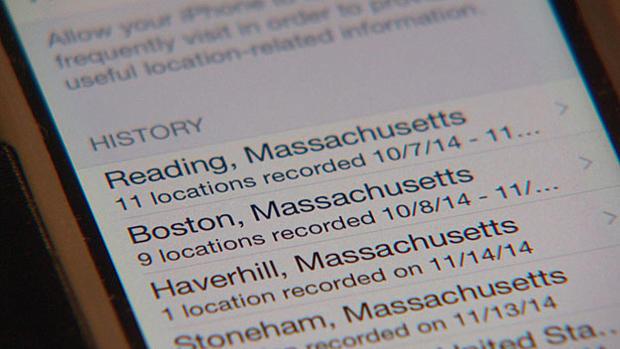
BOSTON (CBS) - Your smart phone sends out personal information, GPS shows where you are, and it's no problem to know which websites you visit. We're married to our devices, but there's a potential danger because it's a fact, we "leak" data all the time. And if you look at a day in the life, you'll be surprised how much.
When the alarm goes off and you start your day, your devices start communicating with the web. One of the first things for many people, checking email and weather. "The weather application knows where I live, it knows where I work, it knows where I travel," says Lee Weiner, a senior VP at Boston's Rapid7, a cyber security company.
He says whenever we use online services and applications we're giving away reams of data. "Just think about how many applications you use. This is happening a lot," he says.
Head to work and your phone connects to Bluetooth, GPS knows where you are and so does the EZ Pass system which also has your credit card information. "All of this is being communicated and stored in a variety of places across the globe," says Weiner.
At work, you connect to corporate WiFi. "Anything you do on Twitter, on Facebook on your personal email is getting routed through that network," says Weiner. Let's say you need to get some work done at lunch so you hook into a coffee shop's wireless network. "You're maybe submitting financial documents through your finance system, maybe you're submitting expenses, maybe you're looking at a sales order form," says Weiner.
And maybe you're not really connected to the shop's WiFi. "It could be somebody else masquerading as that network," warns Weiner. That jeopardizes your credit cards, user name and passwords. Same story if you take an online shopping trip. "They can steal really anything that you're doing online," says Weiner.
For anyone using health apps to measure workouts or steps taken or calories burned, watch out. "All that has to get stored somewhere. The danger of that being out there is that this data may be compromised by an attacker on these services," says Weiner.
Sounds bleak, right?
Well check back here Tuesday and we'll show you concrete steps you can take to protect yourself and your information. It could save you a lot of trouble.
MORE LOCAL NEWS FROM CBS BOSTON